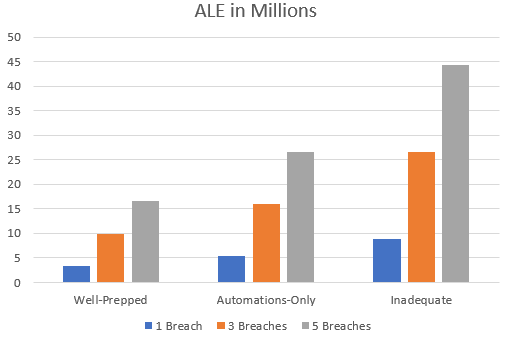
 ALE calculations based on IBM's data.
ALE calculations based on IBM's data.
In 2020, data breaches had an average total cost of $3.86 million, generally taking 280 days to identify and contain, with at least 80% involving or related to customer PII (IBM Security, 2020). In their study, IBM identified that the majority of breaches were caused by malicious attacks, followed by systems glitches and then human error. In responding to these attacks, organizations saw cost mitigations from incident response testing, vulnerability testing, and other cyber security programs. Costs were increased by overly-complex security systems, compliance failures, and security skills shortages (IBM Security, 2020, p. 42).
These wide-ranging security studies are published every year, and they always have similar results. Organizations that have well-defined security programs are less likely to face breaches, and they lose less when breaches do occur. Despite these repeated results, organizations still fail at implementing adequate information security policies. Despite these repeated studies, companies fail to prepare for disaster.
Make no mistake, many security breaches are disasters. They cause losses like earthquakes, tornadoes, or wildfires. Yes, those disasters have more physical results, but the information security world could learn a lot from so-called natural disasters. Disasters, by definition, are "the consequence of the interaction between a hazard and the characteristics that make people and places vulnerable and exposed" (PreventionWeb). Yet, like a security breach, the outcome is directly related to the mitigations emplaced by preparedness. As Dr. Malka Older puts it, "hazards do not automatically cause disasters". Company assets and PII do not have to be affected whether through a hacker's exploit, a misconfiguration, or human error. We can mitigate the risks of loss with appropriate preventative measures.
Of course, most business don't have the resources to turn all attention toward prevention. A company's purpose is to provide a product or service; security is necessarily a byproduct of the company's existence. So, we have to quantify the differences between readiness and being reactive. All organizations operate through an ever-expanding web of interactions with internal and external forces. Maintaining operations requires a balance between reacting to the present and preparing for the future. To achieve that balance, organizations can measure costs through the use of calculating return on security investment (RSOI).
"With a good survey and scoring system for productivity, combined with external measurements of intellectual property value, it becomes possible to quantify risk exposure in a repeatable and consistent manner" (Sonnenreich, 2005). In other words, calculating a company's security expenditures should be a balance between the cost of productivity and intellectual property. Security teams will find it difficult to influence the use of security systems that cost more than these elements. Unfortunately, Sonnenreich also writes that "security almost always comes at the cost of convenience", and that assessment will ring true to anyone that's been forced to restart their computer to install patches. This is why risk-based approaches are important. Business leadership must consider the risk of an attack in comparison to the risk of lost productivity, time, or capability. The costs must be assessed beyond a simple hardware purchase.
Importantly, organizations should also make these assessments with an understanding of their purpose and place in the world. Government resources-provincial, statewide, or regional-can't be assessed versus an expected profit. Government can't be expected to make profit in the first place, so how would they calculate RSOI? In those cases, the outlook would be similar to maintaining a highway. The public-good provided by roads is a sort-of-profit in that it enables the welfare of human lives. A highway destroyed by erosion or earthquakes will disrupt lives in the countless ways that a security breach will disrupt daily operations-especially if the security breach reveals personally identifying information.
"The key to understanding disaster risk is by recognizing that disasters are an indicator of development failures, meaning that disaster risk is a measure of the sustainability of development" (PreventionWeb). Better security is brought about through sustainable technology development-the balance between costs and returns. We can't just buy the newest tech and implement overly-complex systems and expect the programs to work. We can't have tentpole personnel that-if they leave-could tank an entire organization. We have to work toward policies and procedures that people can maintain. We have to craft systems that expect a breach but mitigate the results. This is the concept of defense-in-depth and zero trust taken to their extremes-systems will be compromised, so how do we prevent that from mattering? As Dr. Older says, it's "the interaction between hazard and human settlement or activity that creates a catastrophe."
The humanity within data is the most-important cost we should assess, so how do we limit the results of threat activity toward our fellow humans?
Coden, Michael (2019, May 9). Yes, Virginia, You Can Calculate For Cybersecurity Budgets. Retrieved on February 23, 2021 from https://www.forbes.com/sites/forbestechcouncil/2019/05/09/yes-virginia-you-can-calculate-roi-for-cybersecurity-budgets/?sh=3092ece53ad4
IBM Security (2020). Cost of a Data Breach Report: 2020. Retrieved on February 23, 2021 from https://www.ibm.com/security/digital-assets/cost-data-breach-report/#/pdf
Older, Malka (2021, February 19). The Texas Crisis Shows (Again) There's No Such Thing as a Natural Disaster. Retrieved on February 23, 2021 from https://slate.com/technology/2021/02/texas-no-such-thing-as-natural-disaster.html
PreventionWeb (n.d.) Disaster Risk. Retrieved on February 23, 2021 from https://www.preventionweb.net/disaster-risk/risk/disaster-risk/
Sonnenreich, W., Albanese, J., Stout, B. (2005, January). Return on Security Investment (RSOI): A Practical Quantitative Model. Retrieved on February 23, 2021 from http://infosecwriters.com/text_resources/pdf/ROSI-Practical_Model.pdf